Threat actors are exploiting legitimate AI workflow automation platforms to conduct sophisticated phishing campaigns and deliver malware, according to new research from Cisco Talos - exposing a governance gap that enterprise security teams have largely overlooked.
Researchers observed threat actors weaponizing n8n, a popular AI workflow automation platform, to facilitate phishing campaigns and deliver malicious payloads or fingerprint devices through automated emails. Talos identified an increase in emails abusing n8n from as early as October 2025 through March 2026, with March 2026 volume approximately 686% higher than in January 2025.
Background
N8n is a workflow automation platform that enables users to connect web applications, APIs, and AI model services to sync data, build agentic systems, and execute repetitive rule-based tasks. Its widespread adoption across finance, healthcare, and technology operations reflects a broader enterprise trend: 85% of enterprises were expected to adopt workflow automation tools by 2025, according to PS Global Consulting.
That adoption, however, has outpaced security governance. Manual security processes cannot scale when organizations produce dozens of low-code/no-code (LCNC) applications and RPA automations weekly - and the problem compounds when companies run multiple LCNC and RPA platforms simultaneously. Citizen and automation developers are more prone to unintentional logic errors that introduce security vulnerabilities, while security teams face a new form of shadow engineering with little to no control over the LCNC application lifecycle.
The n8n campaign is the latest example of legitimate productivity and low-code platforms - such as Zapier and Softr.io - being weaponized for phishing and malware delivery. The Acronis H2 2025 Cyber Threat Report similarly found that phishing dominated email-borne threats and that attackers increased their operational use of artificial intelligence across attack workflows.
Details
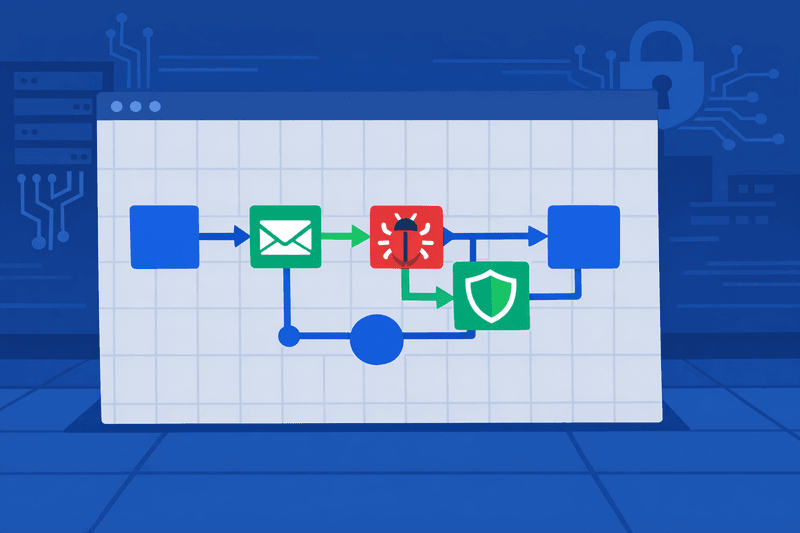
The core technique exploits the trusted reputation of the automation platform itself. Because webhooks mask the source of the data they deliver, they can serve payloads from untrusted sources while appearing to originate from a trusted domain. Since webhooks can dynamically serve different data streams based on triggering events - such as request header information - a phishing operator can tailor payloads based on the user-agent header.
One well-documented campaign involved phishing emails posing as shared Microsoft OneDrive folder notifications. When recipients clicked the embedded n8n webhook link, their browser loaded an HTML page containing a CAPTCHA challenge, which served as a human verification gate to filter out automated scanners. Once the CAPTCHA was solved, a file was silently fetched from an external host. Because the process ran entirely within the n8n domain's JavaScript, the download appeared to originate from trusted n8n infrastructure.
The attack's end goal is to deliver an executable or MSI installer that serves as a conduit for modified versions of legitimate Remote Monitoring and Management (RMM) tools like Datto and ITarian Endpoint Management, establishing persistence by connecting to a command-and-control server. Beyond payload delivery, threat actors leveraged n8n webhooks for device fingerprinting by embedding invisible tracking pixels in HTML emails. This forced the victim's email client to send an HTTP GET request to the webhook URL when the message was opened - automatically capturing the victim's IP address and verifying the email account's activity without requiring any direct interaction.
Cisco Talos researchers Sean Gallagher and Omid Mirzaei stated: "By leveraging trusted infrastructure, these attackers bypass traditional security filters, turning productivity tools into delivery vehicles for persistent remote access."
The attack surface is compounded by structural weaknesses in how automation platforms are provisioned. Attackers created free developer accounts on n8n, which automatically provisioned subdomains under the *.app.n8n.cloud namespace. Because those subdomains belong to a widely recognized service, outgoing emails and web requests from them are treated as trustworthy by many corporate security gateways - allowing attackers to route malicious content through a channel unlikely to raise flags.
The RPA and LCNC security risk extends beyond phishing. A common problem is how bots store credentials - often embedding hardcoded passwords or API keys in scripts - and without strict enforcement of the Principle of Least Privilege, bots may be overprovisioned with access that exceeds their task requirements. Krista Arndt, Associate CISO at St. Luke's University Health Network, warned that third-party SaaS "one-click AI agents" often create service accounts enterprises never see - and if undetected, they are never removed, resulting in what she termed "ghost access, invisible in IGA/IDM, but fully authorized in your environment."
Outlook
Because AI automation platforms are inherently designed to be flexible and trustworthy, Talos researchers argue the security community must move beyond simple static analysis. Rather than blocking entire domains - which would disrupt legitimate business workflows - security teams should adopt behavioral detection approaches that trigger alerts when high traffic volumes target such platforms from unexpected internal sources, or when an endpoint communicates with an automation platform domain outside the organization's authorized workflow inventory.
Analysts expect additional disclosures and potentially mitigations from n8n. Defenders should update detection rules and threat-hunting playbooks to include workflow automation telemetry. Practical mitigations include tightening registration controls, enforcing multi-factor authentication and billing validation, blocking or scrutinizing third-party subdomains in high-risk contexts, and integrating webhook behavior into DLP and email-gateway policies.
Preventive measures such as patching, MFA, and secure gateways remain foundational, yet no perimeter is perfect. Adaptive defenses - including AI-enabled detection, threat hunting, and strong governance of both human and machine identities - are required to contain intrusions. IBM research found that 51% of enterprises now use security AI or automation, and those organizations experience $1.8 million lower average breach costs than those without it, according to the IBM Cost of a Data Breach 2025 report.